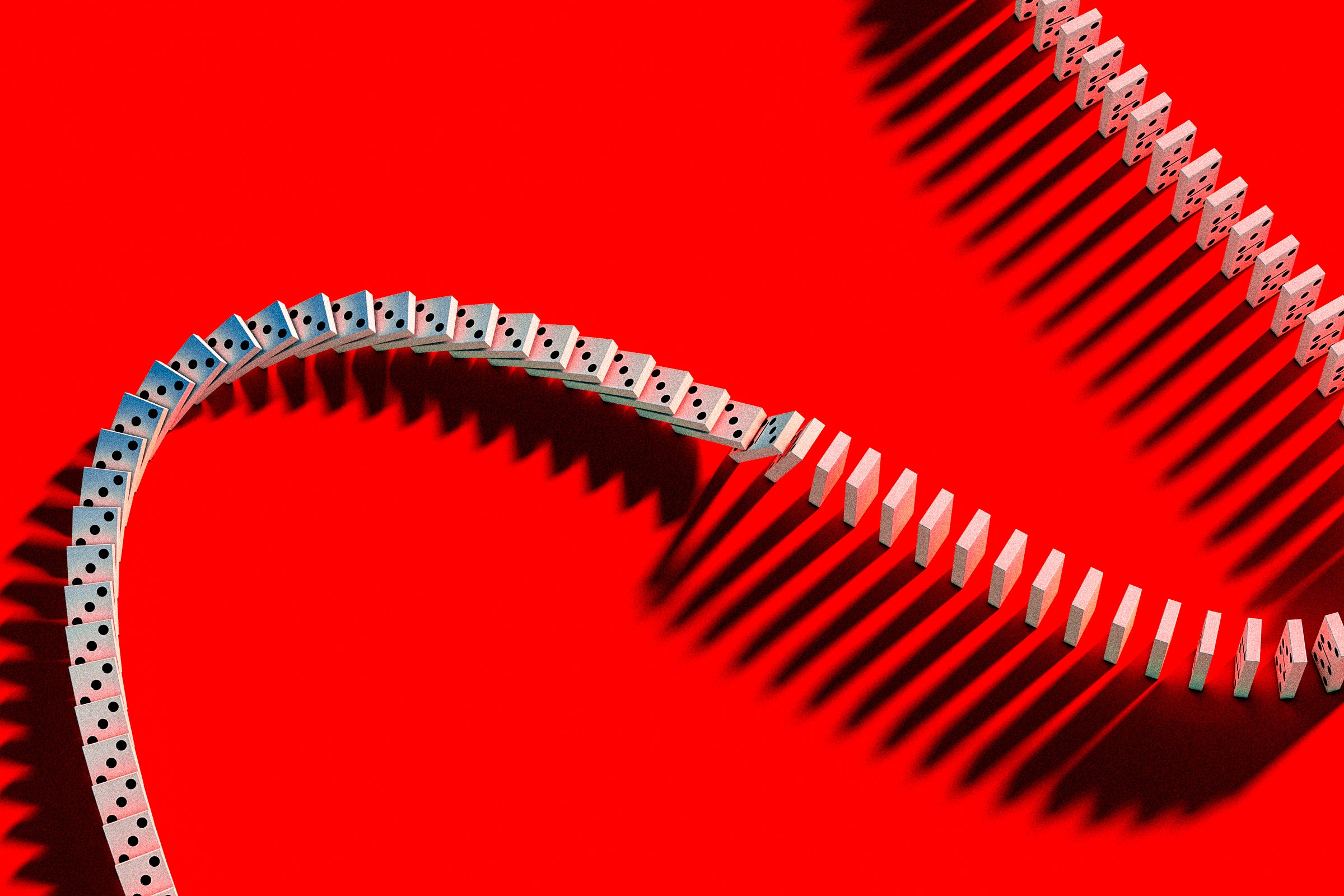
The cybersecurity industry has scrambled in recent weeks to understand the origins and fallout of the breach of 3CX, a VoIP provider whose software was corrupted by North Korea–linked hackers in a supply chain attack that seeded out malware to potentially hundreds of thousands of its customers. Cybersecurity firm Mandiant now has an answer to the mystery of how 3CX was penetrated by those state-sponsored hackers: The company was one of an untold number of victims infected with the corrupted software of another company—a rare, or perhaps even unprecedented, example of how a single group of hackers used one software supply chain attack to carry out a second one. Call it a supply-chain chain reaction.
Today, Mandiant revealed that it found patient zero for that widespread hacking operation, which hit a significant fraction of 3CX's 600,000 customers. According to Mandiant, a 3CX employee’s PC was hacked through an earlier software-supply-chain attack that hijacked an application of the financial software firm Trading Technologies, conducted by the same hackers who compromised 3CX. That hacker group, known as Kimsuky, Emerald Sleet, or Velvet Chollima, is widely believed to be working on behalf of the North Korean regime.
Mandiant says the hackers somehow managed to slip backdoor code into an application available on Trading Technology's website known as X_Trader. That infected app, when it was later installed on the computer of a 3CX employee, then allowed the hackers to spread their access through 3CX's network, reach a server 3CX used for software development, corrupt a 3CX installer application, and infect a broad swath of its customers, according to Mandiant.
“This is the first time we've ever found concrete evidence of a software-supply-chain attack leading to another software-supply-chain attack,” says Mandiant Consulting's chief technology officer Charles Carmakal. “So this is very big, and very significant to us.”
Mandiant says it hasn't been hired by Trading Technologies to investigate the original attack that exploited its X_Trader software, so it doesn't know how the hackers altered Trading Technologies' application or how many victims—other than 3CX—there may have been from the compromise of that trading app. The company notes that Trading Technologies had stopped supporting X_Trader in 2020, though the application was still available for download through 2022. Mandiant believes, based on a digital signature on the corrupted X_Trader malware, that Trading Technologies' supply chain compromise occurred before November 2021, but that the 3CX follow-on supply chain attack didn't occur until early this year.
A spokesperson for Trading Technologies told WIRED that the company had warned users for 18 months that X_Trader would no longer be supported in 2020, and that, given that X_Trader is a tool for trading professionals, there's no reason it should have been installed on a 3CX machine. The spokesperson added that 3CX was not a customer of Trading Technologies, and that any compromise of the X_Trader application doesn't affect its current software. 3CX didn't respond to WIRED's request for comment.
Exactly what the North Korean hackers sought to accomplish with their interlinked software-supply-chain attacks still isn't entirely clear, but it appears to have been motivated in part by simple theft. Two weeks ago, cybersecurity firm Kaspersky revealed that at least a handful of the victims targeted with the corrupted 3CX application were cryptocurrency-related companies based in "Western Asia," though it declined to name them. Kaspersky found that, as is often the case with massive software supply chain attacks, the hackers had sifted through their potential victims and delivered a piece of second-stage malware to only a tiny fraction of those hundreds of thousands of compromised networks, targeting them with “surgical precision.”
Mandiant agrees that at least one goal of the North Korea–linked hackers is no doubt cryptocurrency theft: It points to earlier findings from Google's Threat Analysis Group that AppleJeus, a piece of malware tied to the same hackers, was used to target cryptocurrency services via a vulnerability in Google's Chrome browser. Mandiant also found that the same backdoor in 3CX's software was inserted into another cryptocurrency application, CoinGoTrade, and that it shared infrastructure with yet another backdoored trading app, JMT Trading.
All of that, in combination with the group's targeting of Trading Technologies, points to a focus on stealing cryptocurrency, says Ben Read, Mandiant's head of cyberespionage threat intelligence. A broad supply chain attack like the one that exploited 3CX's software would “get you in places where people are handling money,” Read says. “This is a group heavily focused on monetization.”
But Mandiant's Carmakal notes that given the scale of these supply chain attacks, crypto-focused victims may still be just the tip of the iceberg. “I think we'll learn about many more victims over time as it relates to one of these two software-supply-chain attacks,” he says.
While Mandiant describes the Trading Technologies and 3CX compromises as the first known instance of one supply chain attack leading to another, researchers have speculated for years about whether other such incidents were similarly interlinked. The Chinese group known as Winnti or Brass Typhoon, for instance, carried out no fewer than six software-supply-chain attacks from 2016 to 2019. And in some of those cases, the method of the hackers' initial breach wasn't ever discovered—and may well have been from an earlier supply chain attack.
Mandiant's Carmakal notes that there were signs, too, that the Russian hackers responsible for the notorious SolarWinds supply chain attack were also doing reconnaissance on software development servers inside some of their victims, and were perhaps planning a follow-on supply chain attack when they were disrupted.
After all, a hacker group capable of carrying out a supply chain attack usually manages to cast a vast net that pulls in all sorts of victims—some of whom are often software developers that offer a powerful vantage point from which to conduct a follow-on supply chain attack, casting out the net yet again. If 3CX is, in fact, the first company hit with this sort of supply-chain chain reaction, it's unlikely to be the last.