(CISOPlatform Summit & SACON 2024) Digital Personal Data Protection Act.pdf
- 1. Preparation for DPDP -By Dr. Jagannath Sahoo, Gujarat Fluorochemicals Prabhakar, TNQ Technologies
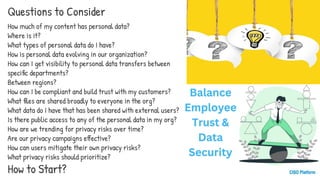
- 4. How much of my content has personal data? Where is it? What types of personal data do I have? How is personal data evolving in our organization? How can I get visibility to personal data transfers between specific departments? Between regions? How can I be compliant and build trust with my customers? What files are shared broadly to everyone in the org? What data do I have that has been shared with external users? Is there public access to any of the personal data in my org? How are we trending for privacy risks over time? Are our privacy campaigns effective? How can users mitigate their own privacy risks? What privacy risks should prioritize? How to Start? Questions to Consider
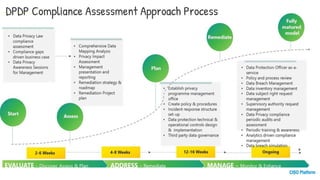
- 6. DPDP Compliance Assessment Approach Process
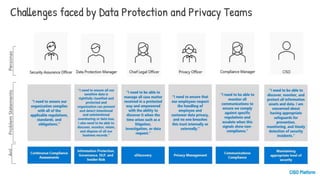
- 7. Challenges faced by Data Protection and Privacy Teams
- 8. Preparing for DPDP Compliance 1 Data Mapping Conduct a thorough audit to identify all the personal data your organization collects, processes, stores and transmits. This comprehensive data mapping exercise is the foundation for compliance. 2 Risk Assessment Analyze the potential risks and vulnerabilities associated with your data practices, taking into account the sensitivity of the information and the likelihood of a breach. 3 Implement and Mitigate Based on your risk assessment, implement appropriate technical and organizational measures to mitigate identified risks and ensure ongoing compliance with the DPDP Act.
- 9. DPDP Compliance Assessment Approach Process
- 10. Enhancing Data Governance for DPDP Compliance Data Loss Prevention Implement robust policies and technical controls to prevent the unauthorized or inadvertent sharing, transfer or use of personal data. Data Retention and Deletion Establish clear data retention schedules and automate the secure deletion of personal information to ensure ongoing compliance. Data Breach Response Develop an incident response plan to quickly detect, report and mitigate data breaches, as required by the DPDP Act.
- 11. Seizing the Opportunities of the DPDP Act Enhanced Consumer Trust By demonstrating a strong commitment to data privacy and security, businesses can build deeper trust with customers and partners. Innovative Data Practices The DPDP Act encourages the development of new, privacy-preserving data processing and management techniques. Competitive Advantages Proactive compliance can give businesses a strategic edge by positioning them as trusted, responsible data stewards. Expanded Market Opportunities Robust data privacy practices may open doors to new business partnerships and markets, both domestically and globally.
- 13. Data protection officer as service Policy and process review Data breach management Data inventory management Data subject right request management Supervisory authority request management Data privacy compliance periodic audits and assessments Periodic training & awareness Analytics driven compliance management. Data breach simulations Data Privacy law compliance assessment. Compliance gaps driven business case. Data privacy awareness sessions for management. Comprehensive data mapping analysis privacy impact assessment Management presentation & reporting remediation strategy & roadmap remediation project plan Establish privacy program management office. create policy & procedures. Incident response structure setup Data protection technical & operational control decision & implementation START ACCESS PLAN Fully Matured Model Evaluate- Discover & Access Plan Address-Remediate Manage-Monitor & Enhance 2-6 weeks 4-8 weeks 12-16 weeks On going Data Privacy Compliance Journey
- 14. 1. Documentation review 2. PII Data Discovery 3. Data flow assessment 4. reporting & next steps Review if current policies & procedures on data privacy and security. Review of data flow diagram and data register (if any) Review of sample contract with third party data processor (if any) Discover PII across enterprise and processes governing the usage and management of the PII data Risk assessment. 1:1 Meeting with key stakeholders Data Gathering workshop with cross functional team. Data flow diagrams and issue identifications Detailed report on organisation DPDP compliance current state & remediation High Level roadmap and DPDP awareness among stakeholders Privacy risk report Data flow maps Assessment Duration (2-6 weeks) Key Deliverable DPDP Compliance report Assessment Coverage ∙ strategy & governance ∙ Privacy by design ∙ PII Data Lifecycle Managemen ∙ Training & awareness ∙ Application & IT Security ∙ Individual Rights Processing ∙ Incident Management DPDP Compliance Assessment Approach Process Methodology
- 15. Scope of the DPDP Act 1 Broad Applicability The DPDP Act applies to all entities that collect, process, store or transmit personal data, regardless of size or industry. This broad scope means every business must carefully evaluate their data practices. 2 Heightened Obligations Data fiduciaries, those who control and process personal data, face significant new obligations to ensure the security, privacy and integrity of the information they handle. 3 Individual Rights The DPDP empowers individuals with greater control over their personal data, requiring clear and informed consent before collection and processing.
- 16. Key Principles of the DPDP Act Consent and Choice Obtaining clear and informed consent from individuals is a core tenet of the DPDP Act. Data fiduciaries must be transparent about how personal data will be used and give individuals meaningful choice in the matter. Data Security and Integrity Data fiduciaries are obligated to maintain the accuracy, security and timely deletion of personal data under their control. Robust data governance policies and technical safeguards are essential. Accountability and Oversight The DPDP Act is governed by a dedicated Data Protection Board, which has the authority to enforce compliance and levy penalties for non-adherence.
- 17. Key Definitions in the DPDP Act Data Fiduciary The entity that determines the purpose and means of processing personal data. They have the primary responsibility for ensuring data privacy and security. Data Processor An entity that processes personal data on behalf of the data fiduciary, but does not have independent control over the data. Personal Data Any information that can directly or indirectly identify an individual, including names, contact details, location data, and online identifiers. Consent A clear affirmative action by the individual to agree to the collection and processing of their personal data, which can be withdrawn at any time.
- 18. Roles and Responsibilities for DPDP Compliance Identify Key Roles Determine which leaders in your organization will be responsible for different aspects of DPDP compliance, such as the CISO, CEO, CTO and other relevant stakeholders. Know Your Data Conduct a thorough audit of your data environment to understand where personal information is collected, processed, stored and shared within your organization. Protect Your Data Classify personal data according to sensitivity and implement adaptive protection measures like encryption, access controls and visual indicators to safeguard the information.